|
|
.png)












|
 |

|
|
'Inside the LPRC IMPACT Conference' 2018
An Eight-Episode Series Presented by
Sensormatic
Assessing The Real-World Impact of LP Efforts
The LPRC Delivers Evidence-Based Solutions and Actionable Results
LPRC
Board of Advisors
Industry Impact & Future Direction
Helping to Steer the Industry's Only Academic Research Effort
Brian Bazer, Sr. Director of Loss Prevention, rue21, &
Chairperson of the LPRC Board of Advisors
Shannon Hunter, VP, LP & Sustainability, Office Depot, & Vice Chair of the LPRC
Board of Advisors
Eric Buttlar, Vice President, Asset Protection, Best Buy, & LPRC Board Member

In our 8th and final episode in this LPNN series, we speak with three members of
the Loss Prevention Research Council's Board of Advisors who are helping steer
the effort with Dr. Read Hayes, Director of the LPRC, and his team.
With years of LPRC involvement, Brian Bazer, Shannon Hunter, and Eric Buttlar
talk about why the LPRC has been so successful over the years and what the
future holds, as the only academic resource in the LP/AP industry bringing
together retailers, solution providers, manufacturers, and government agencies
to solve the problems of today and potential problems of the future.
From utilizing evidence-based research to developing peer relationships,
learn how the LPRC can help you contribute to your organization at a much higher
level.
As a retailer, the LPRC can help you work smarter, not harder, leveraging the
wisdom of the crowd without reinventing the wheel. As a solution provider, the
LPRC allows you to hear directly from the voice of the customer.
Get involved today! Learn more at
lpresearch.org
|
Exclusive Sponsor: |
 |
See more of our 2nd LPRC series
here.
Watch our 1st series
here.
Take the time to learn. As this is the LP/AP academic "Think Tank". |

|
 |

|

|
 |
Johanna Agudelo named
Corporate Asset & Profit Protection Manager for Burberry
Johanna was previously an Operations Manager, NYC for St. Moritz
Security Services, Inc. Prior, she worked at Louis Vuitton for over
three years as Maison Manager and LP Manager, Bloomingdale's for
nine years as LP Manager, Nordstrom as Human Resources Assistant and at
Forever 21 as Assistant Store Manager. She earned her Bachelors of
Science in Criminal Justice from Saint John's University.
Congratulations Johanna! |
Submit Your New Corporate Hires/Promotions or New Position |
 |

|
|
Compass Group Eliminates Asset Protection
Function
Wiping out the last six positions in the US, two AP positions in Canada and the
Senior VP Asset Protection position as well. After going through a number of
transitions over the last couple of years.
They managed over 2,000 food service locations in North America.
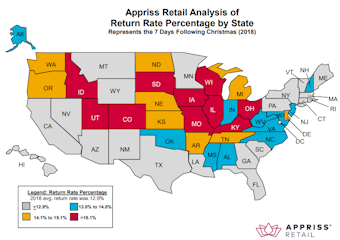
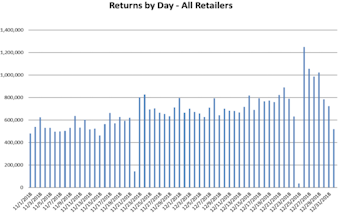
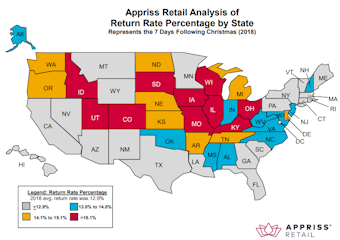
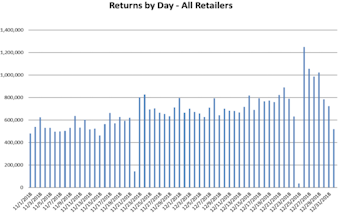
Post-Holiday Returns Changing as Buy-Online-Return-In-Store Grows
Appriss Retail's 2018 Holiday Returns Statistics Unveil Several Unexpected
Trends in Consumer Return Behavior This Past Holiday Season
Appriss Retail, a division of Appriss, Inc., the industry leader in retail
performance improvement solutions, today released its 2018 holiday returns
statistics. With return authorization solutions deployed in more than 34,000
stores across the country, Appriss Retail annually reports on the state of
post-holiday returns in the United States. The company's breadth of retail
clients and deep analytical expertise uniquely position it to draw an accurate
portrayal of this shopping activity during the seven days after Christmas.
"These statistics provide a snapshot of the state of post-holiday returns and
are intended to offer retailers insights on return behaviors and the
opportunities they provide for re-capturing return dollars," said David Speights,
chief data scientist at Appriss Retail. "Foot traffic in stores is very high on
the days before and after Christmas. Our goal is to help retailers optimize
their return processes and offer a positive shopping experience for their
consumers."
FOUR FACTS ABOUT 2018 HOLIDAY RETURNS
globenewswire.com
2 DSW Stores participated in Part I of LPRC/CIS
Security Solutions testing of the CIS Gen5, and the results are in!
 Offenders
were interviewed by members of the Loss Prevention Research Council regarding
the Gen5. Here are some excerpts: Offenders
were interviewed by members of the Loss Prevention Research Council regarding
the Gen5. Here are some excerpts:
Offenders were presented with a high-end hand bag and asked if they noticed any
deterrents on the product. 100% of offenders noticed (See It) the Gen-5
Tether.
While 100% identified the tag as a deterrent (Get It), 80% of offenders
also understood the mechanism of the tether, correctly guessing that the tag had
a built-in alarm that would go off when any part of the tether was cut, or the
entire tether was removed.
In response to the Gen 5 Tether, offenders rated their likelihood of
attempting to steal an item protected by the tether at 1 out of 7, "Extremely
unlikely". Not a single offender was at all
willing to attempt theft of an item protected by this solution. (Fear
It).
Read more here.
The Loss Prevention Foundation (LPF) Announces Newest Associate Level Partner,
Product Protection Solutions (PPS)
  The Loss Prevention Foundation (LPF) announced its newest Associate Level
Partner, Product Protection Solutions (PPS). The Associate level partnership
secures numerous LPQ and LPC certification course scholarships for PPS to
distribute to industry professionals. The Loss Prevention Foundation (LPF) announced its newest Associate Level
Partner, Product Protection Solutions (PPS). The Associate level partnership
secures numerous LPQ and LPC certification course scholarships for PPS to
distribute to industry professionals.
Headquartered in Swansboro, NC, Product Protection Solutions provides both
consultative services and physical loss prevention technologies to support
customer needs. With a combined total of more than 60 years of experience in the
application of AM, RF, and RFID technologies throughout the loss prevention,
electronic article surveillance, and supply chain arenas, the PPS team is a
powerful ally to have at your fingertips.
yourlpf.org
The Next Step in Networked Cameras - AI-Based
Security Apps
Bosch Launches An IoT App Store To Bring AI Surveillance To The Mass Market
With consumer spending on Apple and Google's app stores generating $71 billion
in 2018, it is hardly surprising that networked camera manufacturers have
been itching to get in on the third-party 'App Culture'
The Axis Camera Application Platform (ACAP), Hikvision Embedded Open Platform (HEOP)
and Dahua Open Platform (DHOP) have enabled third-party software developers to
create or adapt analytics to run directly on the IP cameras supplied by the
world's leading manufacturers. But the challenge has been that if you have a
clever application, you need to adapt it to various platforms in order to reach
a broad market.
Cue Bosch and their newly minted SAST (Security and Safety Things) "fully owned
but independent" start-up, which has launched with the intention of "creating a
global industry standard... developing an open operating system... building an app
store." Now in its early stages, the plan is that SAST will hit the market this
year and deliver a "revolutionary open IoT platform for security cameras...
unleashing a new generation of AI-based security apps."
SAST is an Android-based camera operating system, with an app store built across
the top; its objective is to become a default cross-industry OS. How this will
work around the full-service offerings from leading vendors such as Avigilon, or
the security and reputational issues with Chinese manufacturers, remains to be
seen. Right now, SAST is focusing on the Open Security and Safety Alliance
(OSSA) which promises to provide "standards and specifications for common
components including an operating system, IoT infrastructure, collective
approach for data security and privacy, and a drive for improved levels of
performance for security and safety solutions."
forbes.com
Retailers Are Attempting to Improve Inventory
View
A new study suggests retailers may be attempting to improve their inventory
view.
According to the 2019 Retail C-Suite Viewpoint Survey, conducted by retail
research firm Incisiv, JDA and Microsoft, 78% of 221 global c-level retail
executives surveyed said they do not have a real-time view of inventory across
channels. Half of respondents believe they do not have the right platforms and
tools in place to support expanded fulfillment options. In addition, nearly half
(46%) do not trust their data.
Almost half (48%) of respondents are working under the pressure of short-term
goals and 41% say they are combating organizational resistance to change.
"Digital transformation maturity and keeping up with the next evolution of
retail, the intelligent enterprise, will require successfully shedding old
habits and eschewing channel-centric thinking for a more holistic view of
retail. The latest technologies such as cloud, artificial intelligence (AI) and
the Internet of Things (IoT) are the key enablers of this transformation."
chainstoreage.com
Can You Replace the HR With LP? Easily
Putting Humanity into HR Compliance: #MeToo & Confirmation Bias
HR's reputation has taken a hit in the #MeToo era. Rightly or not, HR has been
accused of overlooking, ignoring or even enabling sexually harassing behavior.
Rather than join in the criticism, I'd like to look at the issue from the
perspective of what behavioral economists and psychologists call "confirmation
bias."
Confirmation bias is the tendency to evaluate information with a view to
supporting what we're already inclined to believe, which often consists of what
we perceive to be in our best interest. Subconsciously, we filter information,
selecting and ignoring facts and interpreting ambiguous information in favor of
a preconceived hypothesis.
How does confirmation bias play out in sexual-harassment investigations?
If I'm your company's HR director, and you come to me with a sexual-harassment
complaint, it's my job to investigate and determine what I believe more
likely than not occurred.
However, if the person you are accusing outranks you and me, I may be putting my
job and career at risk if what I find supports your allegations. This is
especially so when there's evidence that people above the alleged bad actor are
complicit in the harassment.
Thus, I may be apt to conduct the investigation and evaluate the evidence in
ways that make it less likely that I'll validate your complaint, regardless
of its veracity. Subconsciously, I want to believe what's safest for me to
believe.
This isn't corruption. It's human nature. As Annie Duke explains in her book
Thinking in Bets (Portfolio/Penguin, 2018), "We are wired to protect our
beliefs even when our goal is to truthseek."
And even when we know better, we may not do better. "Just because you're aware
of confirmation bias doesn't mean you won't succumb to it," said Erin Bair,
J.D., director of training and organization development for Cascade Employers
Association in Salem, Ore. "Sometimes being aware of a bias can give us a false
sense of confidence that it won't affect us."
So what can be done?
No matter how unbiased HR thinks it can be, sometimes it needs the confidence
and strength to say the investigation should be conducted by someone outside the
company."
And if HR has had to conduct performance management with the complainant or had
other interactions with the employee, "then maybe HR should not conduct the
investigation," she added. shrm.org
2019 The Breakthrough Year for Biometric Payment
Cards
Adopted By Millions Around the World in 2019
After a series of breakthroughs in fingerprint sensor manufacturing, new
architectures such as system-on-chip (SOC), and power harvesting in recent
years, biometric payment cards reached the point of widespread testing in
2018.
It seems increasingly likely that payment cards are about to be the second
consumer item widely deployed with embedded biometrics.
The rise of IoT-driven ecommerce and biometric payments in 2019 will require
close collaboration by retailers, IoT providers, and payment providers to
leverage new technologies.
Gemalto SVP Banking and Payment Howard Berg predicts the first commercial
rollouts of biometric payment cards will be next year in the UK and Europe,
with mainstream adoption following in developed markets.
.png) "In
the longer-term, it seems only logical biometrics will take over PIN code for
cards and will also become commonly used in new areas such as authenticating
wearables and other devices. As digital IDs and biometrics become fully embedded
into the consumer purchasing journey, they will become both an identification
step at the stage of check-in rather and an authentication step at checkout.
This means that our digital identity will become our payment token, enabling a
seamless purchasing experience." "In
the longer-term, it seems only logical biometrics will take over PIN code for
cards and will also become commonly used in new areas such as authenticating
wearables and other devices. As digital IDs and biometrics become fully embedded
into the consumer purchasing journey, they will become both an identification
step at the stage of check-in rather and an authentication step at checkout.
This means that our digital identity will become our payment token, enabling a
seamless purchasing experience."
Increased use in programs such as TSA PreCheck and India's Aadhaar is also
contributing to growing public comfort with biometrics, both in the U.S. and
globally, according to Heinze.
IDEX Biometrics CEO Stan Swearingen calls 2019 an "inflection point" for
biometric smart cards. He predicts that dual interface will be used more broadly
as biometrics become available for contactless payments, and that "remote
enrollment will be the key to mass market adoption."
biometricupdate.com
Shutdown Impacting Recalls
Grocery & Food Service Industry Beware
Companies issuing product recalls aren't getting support from the
Consumer Product Safety Commission, which usually spreads the word and also
monitors how the recall is implemented. Companies are often wary of issuing
recalls on their own because they don't want to have to do it a second time if
the CPSC doesn't agree with their evaluation, lawyers say.
wsj.com
Amazon Poses More of a Threat Now Then Ever
Before
"Amazon is less of an e-retailer today than it was a year ago
And that progression isn't going to stop." Who's Next?
And that's exactly what it is a threat plain and simple.
In 2017, Amazon's online retail business accounted for 61% of its revenue. In
2014, it was 77%. Amazon is diversifying, getting into bricks-and-mortar retail
(with the acquisition of Whole Foods), and building out highly profitable
services retailers and other businesses can outsource to Amazon, which include
fulfillment and cloud computing, and the use of the Amazon marketplace.
Amazon powered nearly 34% of total retail sales growth in the US last
year and 65% of US households have an Amazon Prime membership.
Amazon will 'Ramp up on pop-ups & Create more returns and pickup options.
digitalcommerce360.com
Walmart's "Stealth Company" Hiring a CEO
Store No. 8, Walmart's startup incubation arm, is looking to launch a new
tech-centered business, according to a job posting for a CEO spot to develop and
lead a "stealth company."
retaildive.com
What the CEOs Read
Surviving Retail Partnerships
Partnerships are popping up all over the place. With the Khol's Amazon
partnership in '17 almost representing a milestone event and garnering a lot of
media coverage. Both positive and critical.
In today's marketplace populated by smart and savvy entrepreneurs, as well as
established and successful businesses, going it alone may no longer produce
sustainable results. And then there's the whole build or buy argument, solved by
choice #3 - partnering. The need for relevant technology almost necessitates
that a retailer finds partnerships to solve the problem of investing the time
and money to develop its own.
Over the past couple of years, strategic partnerships have become the norm
rather than the exception: Uber and Spotify, IBM and Apple, Walmart and
Microsoft, Versace, Armani and Cavalli with hotel chains, Barnes & Noble with
Starbucks ... and Starbuck's with anyone who's got a pulse.
therobinreport.com
Don't Base Exec Bonuses on Subjective Criteria
Should bonuses paid to CEOs and CFOs be linked to qualitative performance
criteria such as displaying strong leadership, mentoring other executives, and
having a strategic vision?
The answer is no, according to
a recent study I conducted with my colleague Nancy Feng at Suffolk
University. Our analysis of data for S&P 500 companies reveals that employee
productivity, asset productivity,
capital expenditures, and future stock returns are lower when the CEO's
bonus payment depends in part on qualitative criteria.
cfo.com
OSHA Penalties Increasing Once the Government
Reopens
OSHA which is an agency within DOL is one of the few agencies that is fully
funded and operational. On January 15th, OSHA issued a pre-published version
of its Federal Register notice for the increase in civil penalties for
violations of OSHA standards and regulations to adjust for inflation. OSHA
penalties for all classifications will increase by $326.
The 2019 maximum penalties are as follows:
● Other-than-Serious: $13,260
● Serious: $13,260
● Repeat : $132,589
● Willful: $132,589
The penalty increase applies to Federal OSHA states, however, OSHA expects that
states operating their own occupational safety and health program will align
penalty structures with Federal OSHA so that such programs are equally effective
as Federal OSHA.
natlawreview.com
LPRC Podcast Episode - 'Buying EAS Detachers Online as a Shoplifter' ft. LPRC
Sr. Research Scientist Mike Giblin
UK: Bloodbath on high street: More than 175,000 jobs will be cut this year and
23,395 shops will shut as internet sales batter retailers
Express CEO abruptly departs - Humm - Another
Scandal Coming Soon?
Say hi to new NFL sponsor, Pizza Hut Hut
|

Join Agilence President and CEO, Russ
Hawkins, as he discusses the ways to stay innovative in the age of disruption in
the upcoming webinar, "Predicting
The Next Curve: Creating a Culture of Innovation."
Webinar Details
● When: February 13, 2019
● Time: 1:00 PM - 2:00 PM ET
● Presented by: Russ Hawkins, President and
CEO at Agilence
 |
|
|
|
All the News - One
Place - One Source - One Time The D&D Daily respects your time & doesn't
filter retail's reality
|
|

|

 |

|
 |

|
 |

|

|
|
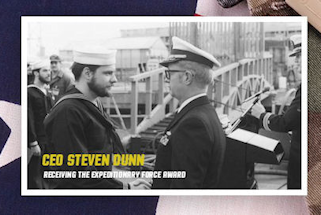
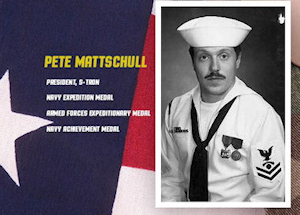
S-TRON's Military Leadership - "Failure Is Not an Option"
At S-TRON,
military leadership has been found to not only bring success but also create an
atmosphere of true partnership with customers across the country.

S-TRON, one of the nation's leading full-service
security providers to national retailers, has intentionally based its business
model on military leadership qualities since the beginning. This leadership
starts at the top with CEO Steven Dunn, who while serving in the Navy
received the Expeditionary Force Award for being part of a multinational
peacekeeping force in in the Beirut Lebanon war zone.
Pete Mattschull, S-TRON's President, decorated with the Navy Expedition
Medal, Armed Forces Expeditionary Medal and the Navy Achievement Medal has been
a driving force at S-TRON since 2003.
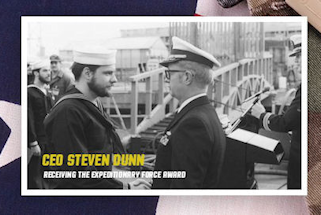
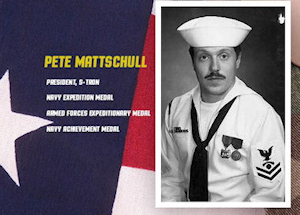
Through rough seas and smooth sailing alike, Dunn and Mattschull have assembled
an ever growing team of military veterans and highly skilled civilians that is
second to none in the security industry. And because of this operational
military environment, S-Tron customers enjoy Respect, Reliability and a
high-level of Communication.
"No customer left behind" is not just
the S-Tron mantra, Pete Mattschull says "it's our way of life".
ABOUT S-TRON
S-TRON is an electronic security integrator for national and regional retailers
with thousands of installation locations and headquarters in Melville, New York.
S-TRON provides outstanding customer service for national retail, grocery
stores, restaurants and C-stores. |

|
 |

|

|
|
Major Fraud Spike in 'Replay Attacks'
Amazon Files Patent for Replay Attack Detection
Security Step Inside Voice Authentication Systems
A patent filed by Amazon for a replay attack detection technology for biometric
voice authentication systems has been published by the U.S. Patent and Trademark
Office.
The filing for "Detecting
replay attacks in voice-based authentication" describes a system in
which a "watermark signal" is included by the device in the captured audio of a
voice authentication factor spoken by the user.
"When a user speaks a voice authentication factor, a unique watermark is played
in the environment in which the user is speaking," the inventors write in the
application. "Accordingly, the watermark should be captured by any surreptitious
recording equipment that is recording at a relative fidelity that is high enough
to accurately reproduce characteristics of the speaker's voice."
If a previously-used watermark is detected in the audio of an authentication
attempt, the system recognizes the audio as a recording, and can optionally
demand another factor, such as a PIN or fingerprint scan. In the various
embodiments presented, the watermark could alternatively be used once, in effect
marking the transaction as current, and never again, or could be produced at a
low frequency to distinguish between a current and previous watermark.
Research from Pindrop indicates that the rapid increase in voice interactions
is being accompanied by a major spike in fraud through the voice channel as
criminals leverage new technology for advanced fraud techniques like
replay attacks.
biometricupdate.com
Largest GDPR Fine To Date
France Hits Google with $57 Million GDPR Fine
Record Privacy Fine Sends Strong Signal to Data Processing Technology
Companies
France on Monday imposed a 50 million euros ($57 million) fine against Google for
violations of the EU's
General Data Protection Regulation, sending a strong to message to the
technology giant that its privacy and data collection practices are
inadequate.
The penalty, levied by the country's
National Data Protection Commission, abbreviated as CNIL, is the largest
fine handed out so far under GDPR, which is intended to better protect
Europeans' personal data.
"The amount decided and the publicity of the fine are justified by the severity
of the infringements observed regarding the essential principles of GDPR:
transparency, information and consent," CNIL says. It has also published a
longer penalty notice, written in French, outlining in full the fine against
Google. govinfosecurity.com
Battling bot-driven gift card abuse
It's a serious and growing problem - and one many retailers fail to recognize
until they or their customers have suffered significant losses.
It's gift card fraud, one aspect of a bot-enabled deception called credential
stuffing: botnets attempting to log into a site to assume an identity,
gather information or steal money, gift cards and/or other goods. Fraudsters use
lists of usernames and passwords gathered from security breaches.
 In the case of gift card fraud, customers frequently blame the retail site or
store they were patronizing when their gift cards or gift card account values
were stolen, damaging the store's brand image and customer loyalties. In the case of gift card fraud, customers frequently blame the retail site or
store they were patronizing when their gift cards or gift card account values
were stolen, damaging the store's brand image and customer loyalties.
Patrick Sullivan, global director of security for intelligent edge cloud
platform Akamai, says over 30 billion malicious credential stuffing login
attempts were made from the beginning of November 2017 until the end of June
2018. These covered a broad range of attacks on all industries, not just
retail.
From approximately 3 billion credential attacks per month in the fourth quarter
of 2017, the amount rose to some 8 billion attacks per month in the second
quarter of 2018.
stores.org
2018's Most Common Vulnerabilities Include Issues
New & Old
Open Source & Rapid-Fire Development & Deployment (Easy & Fast)
WhiteHat Security put together this list of the
most common web exploits used by malicious hackers in 2018, and their list
contains both new vulnerabilities and "classics" that continue to haunt the
waking dreams of security professionals.
The majority of the breaches on the list come from one of two "epicenters" in
software development. The first is in the wide use of open-source tools,
functions, and applications in projects. "Developers can use public APIs to
quickly deliver application functionality that is creating or opening a new
set of vulnerabilities that that customers and the industry have to deal
with," he explains.
The other vulnerability epicenter, Kulkarni says, is the rapid-fire
develop/deploy cycle exemplified by DevOps. "Devops, micro services, and
open source are also contributing a new set or a new kind of vulnerability into
the mix because developers have now more power to push code into production," he
says.
darkreading.com
Shadow IT, IaaS & the Security Imperative
Organizations must strengthen their security posture in cloud environments. That
means considering five critical elements about their infrastructure, especially
when it operates as an IaaS.
Shadow IT, the use of technology outside the IT purview, is becoming a tacitly
approved aspect of most modern enterprises. Yet, with the vast adoption of
software-as-a-service and infrastructure-as-a-service (IaaS) approaches, shadow
IT presents increased security challenges that can create major risk. To further
complicate things, because organizations aren't centrally controlling these
solutions and tools, their vulnerabilities often go undetected for far too long.
If individuals and internal teams continue to introduce outside tools and
solutions into their environments, enterprises will have to adopt a smart path
to ensure they operate securely.
darkreading.com
Navigating the Cyber Crime Scene
Companies in the throes of fighting a cybersecurity incident sometimes corrupt
or destroy digital evidence. After an incident, investigators must use logs,
network activity and other electronic clues to decipher what happened and decide
whether to pay insurance claims or pursue criminal cases. The CISO, working with
internal and external lawyers, should set rules about what kind of evidence
should be preserved, experts say.
Technology staff should practice, too, says Kip Boyle, chief executive of
consulting firm Cyber Risk Opportunities LLC. "Policy is important -- and
training."
Preserving Digital Evidence in the Heat of a
Cyberattack
Companies fighting a cyberattack must collect digital evidence quickly before it
disappears, either erased by the intruder or overwritten during the company's
typical operations.

Good response in the midst of a cyberattack requires clear policies created
during calm times well before an incident occurs. Companies should have a plan
with specific technological steps to preserve digital clues for insurance claims
and criminal cases that might be filed later, experts say.
At a physical crime scene, the first police officer who arrives knows to secure
the area and avoid contaminating the scene by, say, touching objects.
In a cyber incident, first responders should take similar care.
Attackers and their tools must be isolated, he said. Abruptly shutting down a
server or turning off a network could destroy systems logs or eliminate the
chance to capture details about the state of the equipment during the attack.
Laying out a clear order of operations, with thresholds for certain actions,
will help technologists stay cool in an attack, Mr. Melendres said.
cybersecurity.cmail20.com
Director of IT Security Posted for Peets Coffee
in Emeryville, CA
The Director of IT Security is responsible for establishing and
maintaining a corporatewide information risk management program to ensure that
information assets are adequately protected.
peets.icims.com
172 Cos. of S&P 500 Haven't Disclosed How They
Manage Cybersecurity Risks
As Requested By SEC - of Public Companies
First AI Diamond Buying Tool Lets Consumers 'See'
True Diamond Quality Online Before They Buy
|
 |
|

|
|
|
|
How to
Check What Programs Are Draining Your Laptop's Battery
Is your laptop
battery dying too fast? Here is how to determine the cause, if you have Windows
10. You will need to open your Task Manager. Just right-click the Start button
or taskbar and click Task Manager. In Task Manager click on the Processes tab
where you will see a section called Power Usage and Power Usage Trend. (If you
don't see these columns listed, right-click in the header and click on them.)
Keep in mind you must have the latest version Windows 10 with the October 2018
update. For some users, it may take 60-90 second to the data in this section to
populate. You will then be able to see what programs are draining your battery
so that you can uninstall or end them to increase your battery potential. |
|
 |
|

|
|

|
|
Graeter's Tells Online Customers Credit Card Info
May Be Compromised
Graeter's, the Cinncinnati-based ice cream chain, is telling thousands of
customers that their credit card information might have compromised in a data
breach.
WLWT reports that the company sent notices to 12,000 customers who purchased
goods on its website in 2018, tellng them unauthorized charges have been
reported.
According to the news station, purchases at the chain's brick-and-mortar stores
were not affected.
Company officials said the problem on an "unauthorized code" added to the
checkout page from June 28 through Dec. 17 of last year.
"We do not know if the notice recipients' card numbers were in fact compromised,
but to be safe, we are notifying anyone who made a purchase during the time that
the malicious code was present," Graeter's President and CEO Richard Graeter
said in a statement. "We have no information about any other breaches. This
breach only involved our online store graeters.com.
lex18.com
Bots, Specialization Supercharging ATO Attacks
Over the past several years, fraudsters have increasingly targeted merchants by
using stolen login credentials to take over customer accounts. Account takeover
has become all too common for e-commerce businesses, but, a new report says
criminals have found a way to supercharge this already thorny problem: botnets.
Account takeover attacks grew by 31 percent from 2017 to 2018, according to
antifraud technology provider Forter. Considering the number of stolen login
credentials circulating and how easily they can be obtained, this is
unsurprising. Just today, security researcher Troy Hunt unveiled one cache
(called "Collection #I") uploaded to cloud service MEGA containing nearly 773
million unique email addresses and more than 21 million unique passwords that
have been aggregated from multiple breaches. Dumps like these are common and are
the fuel enabling ATO to explode.
Only a select group of fraudsters, however, are engaging in this type of fraud.
By aggregating and analyzing the data of its clients, Forter found that 80
percent of the ATO attacks on a typical website are launched by only 10 percent
of the fraudsters attacking each site. Using bots, a relatively small number of
bad actors are able to automate the process of trying stolen login credentials
to gain access to accounts at scale.
cardnotpresent.com
Amazon Fights Image as Retail Goliath
Amazon wants to change its image as a retail goliath and have people think of it
as a platform for supporting small businesses. On Friday, it issued a
press release to support that notion.
Amazon particularly wants to be seen by lawmakers and regulators as being pro
small-business and as contributing to job-growth, two areas politicians are
especially keen on. "In 2018, Amazon introduced the Small Business Impact
Report. According to the report, small and medium-sized businesses selling in
Amazon's stores are estimated to have created more than 900,000 jobs worldwide,"
Amazon bragged.
ecommercebytes.com |
|
|
|
 |
|

|
|
 |
|

|
|

|
|
Philadelphia, PA: Court documents detail alleged
$130,000 credit card scam at Kmart stores in South Jersey and beyond
Even as the Kmart chain lost stores and customers, the struggling discounter
could count on one group of customers at its Delaware Valley stores. But those
shoppers were scammers, federal authorities allege. A criminal ring allegedly
used stolen identities to obtain credit cards in the names of unsuspecting
victims, then sent its members into area Kmarts to make purchases of more than
$130,000.
Two of the group's members, including a woman charged this month, are accused of
making fraudulent purchases worth more than $11,000 at four South Jersey Kmarts.
According to court records, ring members allegedly obtained CitiBank Sears
credit accounts with ID information stolen from unsuspecting consumers. Other
participants, called runners, had their names added to the fraudulent accounts
and were sent on shopping trips to the Sears-owned Kmarts.
courierpostonline.com
West Brandywine Township, PA: 11 brand-new
motorcycles stolen from dealership; valued at nearly $80,000
Police were dispatched to Cycle Max on Horseshoe PIke, early Friday morning
shortly before 4 a.m. for a burglar alarm activation. Police discovered the
front door smashed and 11 brand-new dirt bikes (Honda, Yamaha and Kawasaki)
stolen from the show room. Police say the description of the suspect's vehicle
is a red pick up truck, possibly a Chevy or Dodge, with a gray enclosed box car
hauler type trailer.
dailylocal.com
Lehi, UT: Multiple Grab & Run robberies of AT&T,
Verizon stores prompt chase
Groups of men rush stores
An attempted robbery of a cellphone store in Lehi prompted a police pursuit on
I-15 Sunday afternoon, and officials said multiple jurisdictions may be
investigating similar incidents. Police were alerted to an instance of
suspicious activity at the AT&T store. A group of men had tried to enter the
store, but the store was closed. Call said similar incidents had previously been
reported by other police departments, including West Jordan and South Jordan.
Scanner traffic also indicates incidents may have taken place in Taylorsville
and Sandy, with the men either attempting to enter or entering stores such as
AT&T and Verizon, grabbing multiple phones, and fleeing. Officials have not yet
released a description of the suspects or the suspect vehicle. Gephardt Daily
will have more on this developing story as information is made available.
gephardtdaily.com
San Francisco, CA: Merchants are at wits' end
with shoplifting in Hayes Valley
Hayes Valley is a haven for shoppers and al fresco diners, but trendiness and an
abundance of retail stores draws a sinister type: petty thieves. Owning a small
business in a pricey city like San Francisco is challenging enough, but
shoplifting "is the thing that deflates me the most," said Elizabeth Leu, the
owner of Fiddlesticks, children's clothing and toy store in Hayes Valley. "It
feels like someone running into your house and grabbing your throw pillows." In
the span of a year, Leu estimates between $6,000 and $10,000 worth of
merchandise is pilfered from her shop, with about two thefts occurring each
month. Leu says she has little recourse. Often the items thieves grab are not
worth enough to qualify as grand theft, which has a minimum threshold of $950,
and filing petty theft claims only increases the business owner's liability
insurance. Between Jan. 18, 2018 and Dec. 18, 2018, a total of four theft crimes
were reported in Hayes Valley, of 420 total in San Francisco. By comparison,
there were 17 reported thefts in the Tenderloin, and 24 in the Mission.
sfgate.com
Berkeley, CA: Young's Backpacking hit for 89 jackets in
Grab and Run; total value of $5,185
UK: Shopkeepers are being forced to lock up HONEY to stop
thieves stealing it to sell for up to $470 a jar to wealthy Chinese buyers
|
|
|
|

|
|

|
|

|
Orland Park, IL: Orland Square Mall shooting: 1
killed, 1 wounded as police search for gunman
 Police
continue to search for the gunman who shot and killed an 18-year-old man and
wounded another person at Orland Square Mall Monday night. The ATF is assisting
police with the investigation, as well as the South Suburban Major Crimes Task
Force. Police released a vague description of the shooter, saying he is an
African-American man, about 20 years old, about 6 feet one inch tall and wore
dark clothing and blue jeans. Police said they believe the shooter knew the
victim. At Orland Square Mall, surveillance cameras captured the chaos as
shoppers and workers ran. Authorities said gunfire erupted at 6:40 p.m. at the
mall's food court. Police said an 18-year-old man was shot in the chest by an
unknown gunman. The victim staggered a short distance before police said he
collapsed in front of shoppers. He later died at a hospital.
abc7chicago.com Police
continue to search for the gunman who shot and killed an 18-year-old man and
wounded another person at Orland Square Mall Monday night. The ATF is assisting
police with the investigation, as well as the South Suburban Major Crimes Task
Force. Police released a vague description of the shooter, saying he is an
African-American man, about 20 years old, about 6 feet one inch tall and wore
dark clothing and blue jeans. Police said they believe the shooter knew the
victim. At Orland Square Mall, surveillance cameras captured the chaos as
shoppers and workers ran. Authorities said gunfire erupted at 6:40 p.m. at the
mall's food court. Police said an 18-year-old man was shot in the chest by an
unknown gunman. The victim staggered a short distance before police said he
collapsed in front of shoppers. He later died at a hospital.
abc7chicago.com
 Billings,
MT: Man shot and killed by Billings Police fired at Officers Billings,
MT: Man shot and killed by Billings Police fired at Officers
A man running from Billings police pulled a gun on an officer before he was shot
dead Sunday afternoon, Billings Police Department Chief St. John said during a
Monday morning press conference. Police were investigating a report of someone
trying to sell stolen guns at a pawn shop when 26-year-old Chance Mavity ran
from them, St. John said. Two officers fired at Mavity 19 times, and Mavity
fired back five times, for a total of 24 shots fired in the downtown alleyway,
St. John said. Mavity was a registered violent offender with previous assault
charges who was wanted for absconding warrants and a probation and parole
violation, St. John said.
billingsgazette.com
Champaign, IL: One person hospitalized after shooting at
C-store
Robberies, Incidents & Thefts
Bart Township, PA: Armed robber confronted at
store
Restrained until State Troopers arrive
State police said the accused robber, 45-year-old David Whitton, went into
Sunrise Grocery on the 100 block of Rosedale Road in Bart Township around 5:30
p.m. Friday. He displayed a handgun and tried to take money from the register,
according to state police. Troopers said the store owner and a family member
confronted Whitton and kept him there until authorities arrived. Whitton was
charged with robbery and aggravated assault, state police said.
wgal.com
Update: Oshtemo, MI: Armed Meijer customer could
face charges
A Meijer shopper who drew his gun and opened fire at a fleeing shoplifting
suspect could now face charges of his own. The incident happened at the West
Main Meijer on January 5th. The shoplifter was not hit and managed to escape.
Kalamazoo County Undersheriff Jim Van Dyken says they are asking the prosecutor
for a warrant charging the shopper with reckless discharge of a firearm.
Michigan law only allows a gun owner to use the weapon when he or she feels they
are threatened with injury or death. The justifiable use of lethal force depends
on the circumstances and those will certainly be reviewed by the prosecutor's
office before deciding whether or not to file charges.
wkzo.com
Brentwood, TN: Shoplifter caught on camera
shoving guitar down pants
A Brentwood store owner was shocked to see a Fender guitar swiped after a man
shoved it down his pants and headed out the door. The owner said the shoplifting
took place at the Lane Music in Brentwood on Saturday afternoon. Brentwood
Police are investigating. The Fender left the building down someone's pants. A
man in a blue cap and big gray coat was caught on camera Saturday.
"We left the guy alone for maybe three minutes," said Laughlin. "He adjusts his
coat. You can see he'd undone his pants. You can see the guitar neck go into the
pant leg, and he adjusts the body on his side. He redoes his pants and covers it
with his coat. If you watch, he doesn't bend his left knee afterward. You can't
see the guitar."
kctv5.com
Trussville, AL: Knife-wielding shoplifter attacked Belk
Loss Prevention officers
Kay Jewelers in the Capitola Mall, Capitola, CA
reported an External Switch on 1/16, item valued at $2,899
Kay Jewelers in the Central Mall, Port Arthur, TX reported a Grab & Run on 1/21,
item valued at $2,799
Fire/Arson
Memphis, TN: Fire affects operations, shipments
at Amazon's Receiving Center
A fire has affected shipments and operations at Amazon's new $70 million Memphis
receive center. "There was a conveyor belt that caught fire there and it was
confined to the belt and some content," Memphis Fire Department spokesman Lt.
Wayne Cooke told The Daily Memphian on Monday. No part of the
615,440-square-foot structure was burned by the fire that occurred Friday, he
said. But some online sellers who ship their products to Amazon's receive center
at 3292 E. Holmes were informed by Amazon shipments will be affected.
dailymemphian.com
Sentencings
Dayton, OH: Three Teens sentenced to 9 years in
AT&T store robbery
The robbery, which occurred in February 2018, saw seven defendants hold
customers and store employees on the ground at gunpoint. Six of the defendants
were juveniles at the time of the robbery but 5 of those case were transferred
to adult court. On Friday, three of teens were sentenced to 9 years in prison.
Two other defendants were also found guilty and will be charged next week.
hhcourier.com
Maryland man gets 10 years in prison for stealing 10 packs
of cigarettes and trying to sell them
for money and gas
|
|

|
| |

|
|
•
AT&T - Lehi, UT - Burglary
•
C-Store - San Antonio, TX - Armed Robbery
•
C-Store - Wilmington, DE - Burglary
•
C-Store - Orlando, FL - Robbery
•
C-Store - Bart Township, PA - Armed Robbery
•
C-Store - Washington County, MD - Armed Robbery
•
Cellphone store - Queens, NY - Armed Robbery
•
Dollar General - Columbia, SC - Armed Robbery
•
Gas Station - University Heights, OH - Armed Robbery
•
Gas Station - Bellevue, WA - Armed Robbery
•
Motorcycle Dealer - West Brandywine Township, PA -
Burglary
•
Motorcycle Dealer - Henrico, VA - Burglary
•
Restaurant - San Francisco, CA - Burglary
•
Verizon - Sandy, UT - Robbery
|
|
|
Daily Totals:
•
9 robberies
•
5 burglaries
•
0 shootings
•
0 killings
|
|

 |
|

|
|
|
|
None to report. |
|
Submit Your New Hires/Promotions or New Position |
|

|
|
.jpg) |
|

|
|

|
|
Featured Job Spotlights
 |
Asset Protection Director, Analytics & Fraud Management
Pataskala, OH
The Asset Protection Director, Analytics & Fraud Management will be responsible
for leading teams focused on delivering insights and managing fraud risk for the
enterprise through the use of advanced technology and statistical analysis. The
Analytics & Fraud Management teams will serve multiple internal customers at the
Ascena level and within the brands...
|
|
 |
District Loss Prevention Manager
Eastern PA/NJ
The District Loss Prevention Manager ensures shrinkage control and improves
safety in the stores through proper investigation and training. This position is
responsible to provide feedback, guidance and protection for our Team Leaders
and Associates. This role has oversight and responsibility for approximately
15-20 store locations...
|
|

|
Asset Protection Supervisor
Middleton, WI
An individual who is committed to safeguarding the assets of our brand through
the education and training of associates, implementation of effective policies
and the leveraging of existing and new technology. This position will be
responsible for:
● Maintaining the safety and security and overseeing the Asset Protection
offices at our Middleton and DeForest campuses...
|
|
.png) |
Loss Prevention Investigator
Media, PA
Wawa is looking for an accomplished Loss Prevention Investigator with an
undergrad degree in Criminal Justice and previous experience in the retail
industry (Multi-Unit).
The Loss Prevention Investigator is responsible for utilizing proper
investigative techniques and act as the primary liaison with field operations
management...
|
|
 |
Retail Security and Safety Specialist
Multiple Locations
This job contributes to REI's success by ensuring the security and safety of
your store team and members by providing a presence on REI property and events.
Activities include but are not limited to: fostering partnerships with and
training store management and staff and taking action to address shrink and
security. Models and acts in accordance with REI's guiding values and mission.
Apply now for positions in: Soho, NY Washington D.C. San Francisco, CA Portland,
OR Bellevue, WA...
|
|
 |
Regional Safety and LP Specialist
Miami, FL
The Safety and Loss Prevention Specialist is a subject matter expert responsible
for partnering with both our corporate stores and franchise store operations to
improve the safety and training processes. This includes reducing motor vehicle
accidents, reducing work-related injuries, and ensuring OSHA / DOT compliance
through the implementation of corporate or franchisee plans in accordance with
local, state, and federal rules and regulations...
|
Featured Jobs
To apply to any of today's Featured Jobs, Click Here
|
|
 |
|

|
|
|
|
Today's
Daily Job Postings from all around the net - Appearing today only
To apply to today's Internet Jobs, Click Here
|
|
Sponsor Today's Internet Jobs |
|

|
|
 |
|

|
|
|
|
Job Search Tips: Ace Your
Interview with $11, Perfect Your Cover Letter, and Get Your Resume Past the ATS
|
|
|
|

|
|
Got a picture of your team on your cell phone?
Send it to us!
 |
|

|
|

|
|
Repetition is one of the keys to success. Developing and evolving your approach,
your message, your actions and processes and focusing on repetitively delivering
them, you'll be able to almost transcend your message and focus on its delivery
as opposed to its action. We all have core things we do every day and if you can
develop repetitive responses, that ensures continuity, you can then begin to
master what you do and truly make an impact on the group you're working with.
Just a Thought,
Gus
 |
|
We want to post your tips or advice... Click here |
|
|
|

|
|
Not getting the Daily? Is it ending up in your spam folder?
Please make sure to add d-ddaily@downing-downing.com to your contact list,
address book, trusted sender list, and/or company whitelist to ensure you
receive our newsletter.
Want to know how?
Read Here |
|
|
|

|
|
 |
.png)
















































 Offenders
were interviewed by members of the Loss Prevention Research Council regarding
the Gen5. Here are some excerpts:
Offenders
were interviewed by members of the Loss Prevention Research Council regarding
the Gen5. Here are some excerpts:
.png)















.jpg)


.png)